I wanted the MDS switches to finally be added to TACACS so that the backup scripts can run with the TACACS login they have for the standard routers/switches. Here’s the code used (note that the fallback to local auth is also enabled if tacacs is unavailable):
tacacs+ enable tacacs+ distribute tacacs-server key whatevs-key tacacs-server host 10.222.222.222 tacacs+ commit aaa group server tacacs+ tacacs-group1 server 10.222.222.222 aaa authentication login default group tacacs-group1 local aaa accounting default group tacacs-group1 local
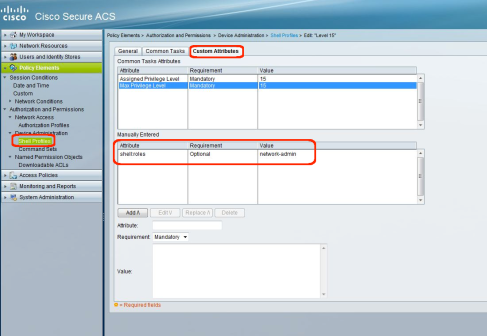
On Cisco ACS 5.x you need to add an option to the shell profile you use for TACACS. In my case I just added the attribute to the standard profile which gives ‘level 15’ privilege to passed authentications for other IOS devices.
Probably easier to show you in an image (below), but for MDS switches to work with ACS 5.x you need to add :
attribute -> shell:roles requirement-> Optional value -> network-admin